Windows firewall squeezes into USB key
May 29, 2007 — by LinuxDevices Staff — from the LinuxDevices Archive — 12 views [Updated Jun. 1] — Yoggie Security Systems has squeezed a hardware firewall for Windows into a USB key sized form-factor. The “Yoggie Pico” runs Linux 2.6 along with 13 security applications on a 520MHz PXA270, a powerful Intel processor popular in smartphones and high-end consumer devices.
[Updated Jun. 1] — Yoggie Security Systems has squeezed a hardware firewall for Windows into a USB key sized form-factor. The “Yoggie Pico” runs Linux 2.6 along with 13 security applications on a 520MHz PXA270, a powerful Intel processor popular in smartphones and high-end consumer devices.


Yoggie Pico
(Click each image to enlarge)
 Yoggie Gatekeeper (Click for details) |
digg this story |
The Yoggie Pico is a spectacularly miniaturized version of the company's original Yoggie Gatekeeper product (pictured at left), which shipped nine months ago and is also based on the Intel PXA270 processor. Both products aim to offload firewall functions to a separate device, in order to increase security and performance of the host PC, and save users from confusing security-related pop-up messages.
CEO Schlomo Touboul explains, “Internet security software running on Windows takes a lot of time to boot, and uses a lot of CPU to scan. It gets fatter and fatter with every update, and as a result, the Windows machine gets slower and slower. The idea of Yoggie is, 'Let's have a second computer, and screen traffic before it reaches the PC.'”
How does it work?
The original Gatekeeper sported a pair of RJ-45 jacks that allowed it to be connected in-line between the network and a PC running any OS, similar to traditional hardware firewalls. Alternatively, it could be connected via its full-speed (12Mbps) USB port, and used in conjunction with low-level Windows drivers that “hi-jack traffic at layers 2-3, below the TCP/IP stack, and route it to USB,” Touboul explained.
The Pico eschews the Gatekeeper's bulky RJ-45 ports, while upgrading USB connectivity to a high-speed (480Mbps) interface. “On a 100Mbps Ethernet, you can barely notice it's there,” Touboul said.
One nice benefit to the USB-plus-host-driver approach is that it works not only with wired networks, but for any network interface on the host PC, including dial-up, WiFi, or even GPRS add-in cards, Touboul said. Drivers for Linux and MacOS X are planned, he confirmed.
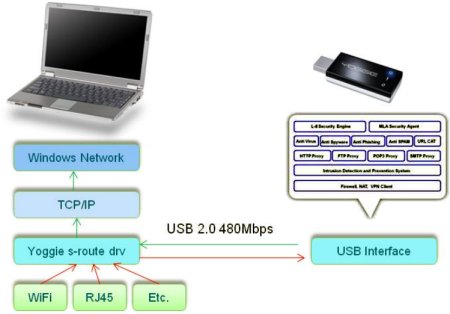
Yoggie Pico architecture
(Click to enlarge)
What does it do?
When plugged into a host PC's USB port, the Yoggie Pico first uses the open source U-Boot bootloader to copy its Linux-based OS and application stack from secure, read-only flash memory onto a separate flash-based boot device, Touboul said. Thus, regardless of what attacks the device may endure, it should always boot up in a pristine state.
The second flash device may well be a NOR flash device capable of supporting XIP (execute-in-place) or another fast-bootup scheme, given that the Pico is said to boot significantly faster than the earlier Gatekeeper — 40 seconds, including launching the 13 applications, compared to 105 seconds for the original Gatekeeper, according to Touboul.
Once running, the Pico establishes an SSL (secure sockets layer) http connection to Yoggie's central servers, where it checks for updated firewall policies and rule sets, Touboul said. It subsequently checks every every five minutes, by default.
A secure browser-based interface allows users to tune operational parameters, and access system status information. According to Touboul, “There is no ssh, no nothing into the Yoggie. The Web interface is the only interface, and it offers some nice graphs and reports about what Yoggie was doing for you over the last week.”




Yoggie's browser-based interface
(Click each screenshot to enlarge)
The Pico actually runs 13 separate security applications, with typical CPU usage ranging between 35 and 50 percent, Touboul said. The stack has knowledge of various file types, such as Word attachments and Java executables, and can fluff up zip and other compressed files on the fly for analysis prior to passing them to the host PC.
Three of Yoggie's applications were licensed from third parties, while half a dozen were written in-house, and another four derived from open source software packages. In particular, Touboul cited the snort intrusion detection and HAVP (HTTP anti-virus proxy) packages as key components of the stack.
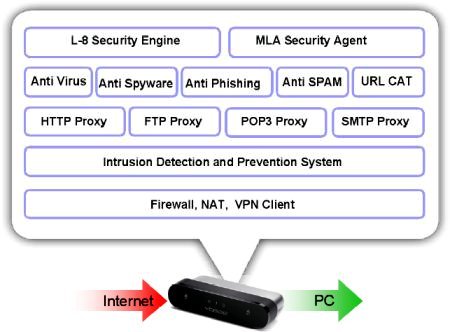
The Yoggie Pico's firewall stack
(Click to enlarge)
Stack components, according to Touboul, include:
- Anti-Spam
- Anti-phishing
- Antispyware
- Antivirus
- Parent control system
- Transparent email proxies (POP3; SMTP)
- Transparent web proxies (HTTP; FTP)
- Intrusion detection system
- Intrusion prevention system
- Firewall
- Adaptive security policy
- Multi-layer security agent (Patent pending)
- “Layer-8” security engine (Patent pending)
What's under the hood?
 Gumstix Verdex (Click for details) |
The Pico is based on a highly miniaturized single-board computer (SBC) with no less than 12 layers inter-connected via blind vias, Touboul said. Given its USB-key form factor, the Pico's SBC appears to be about half the size of Gumstix's recently introduced Verdex (pictured at right), an 8-layer design that was previously the smallest PXA270-based board we've seen.
The Pico is based on an Intel PXA270 processor clocked at 520MHz. It has 128MB of RAM, and 128MB of flash memory, apparently divided between 64MB of secure flash and 64MB of boot flash (as described above).
The Pico SBC's two flash chips appear to reside on a separate add-in card connected via surface-mount connectors. This could give the design some expandability, should storage needs grow and/or memory sizes/prices fall.
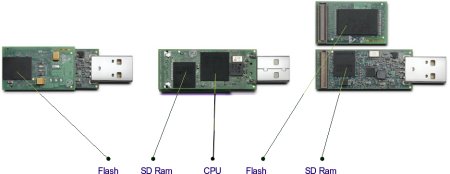
The Pico's SBC relegates flash to a daughtercard
(Click to enlarge)
Rather than using the PXA270's full-speed USB interface, the Pico incorporates an off-chip USB controller capable of high-speed (480Mbps) operation.
According to Touboul, ten engineers worked nine months on the combined hardware/software design, with cooling proving to be “quite a challenge,” albeit not an insurmountable one. “It can run pretty hot, but not hot enough to cause problems,” he said.
On the software side, Yoggie developed its Linux stack in-house, starting out with Debian Linux packages.
Touboul stated, “The growing threat from Internet borne attacks and the negative user experience with heavy software security suites has led us to develop the Yoggie Pico series. Now users can offload security tools from their computer and regain their application performances while trusting the highest security level provided by Yoggie Pico.”
Availability
The Yoggie Pico will ship the first week of June, priced at $180 with a year's subscription to updates, according to the company. Subscriptions will cost $30/year thereafter. Distribution channels are being finalized, but will include big-box retailers like CompUSA and Fry's (Outpost.com), Touboul said. Dexxon Digital Storage, Inc. (DDSI) will handle distribution in North America.
Also available for $200 will be a “Pro” version targeting the enterprise market. It adds VPN features, and is designed to fetch firewall updates from a local enterprise server rather than Yoggie's central servers.
This article was originally published on LinuxDevices.com and has been donated to the open source community by QuinStreet Inc. Please visit LinuxToday.com for up-to-date news and articles about Linux and open source.